Configuring User Registration
User self-registration lets end users create their own accounts in AM. You can configure AM to perform user registration, or you can delegate user registration to IDM.
This section covers configuring AM to:
Perform user registration itself. See "To Configure User Self-Registration by AM".
Delegate user registration to IDM. See "To Delegate User Self-Registration to IDM".
Although you can configure user self-registration without any additional security mechanisms, such as email verification or KBA security questions, we recommend configuring the email verification service with user self-registration at a minimum.
In the AM console, configure the Email Service as described in "Configuring the Email Service".
Navigate to Realms > Realm Name > Services and select the User Self-Service service.
Select the User Registration tab.
Enable User Registration.
Enable Captcha to turn on the Google reCAPTCHA plugin. Make sure you have configured the plugin as described in "Configuring the Google reCAPTCHA Plugin".
Enable Email Verification to turn on the email verification service. We recommend you leave Email Verification enabled, so users who self-register must perform email address verification.
Enable Verify Email before User Detail to verify the user's email address before requesting the user details.
By default, the user self-registration flow validates the email address after the user has provided their details. Enable this setting for backwards-compatibility with self-registration flows configured in OpenAM 13 or 13.5.
Enable Security Questions to display security questions during the self-registration process. If you enable security questions, the user is presented with the configured questions during the forgotten password and forgotten username flows. The user must answer these questions in order to reset their passwords or retrieve their usernames.
In the Token LifeTime field, set an appropriate number of seconds for the token lifetime. If the token lifetime expires before the user self-registers, they will need to restart the registration process.
Default:
300seconds.To customize the User Registration outgoing email, perform the following steps:
In the Outgoing Email Subject field, enter the subject line of the email.
The syntax is
lang|subject-text, wherelangis the ISO-639 language code, such asenfor English, orfrfor French. For example, the subject line values could be:en|Registration Emailandfr|E-mail d'inscription.In the Outgoing Email Body field, enter the text of the email.
The syntax is
lang|email-text, wherelangis the ISO-639 language code. The email body text must be all on one line, and can contain any HTML tags within the body of the text.For example:
en|Thank you for registering with example.com! Click <a href="%link%">here</a> to register.
In the Valid Creation Attributes field, enter the attributes the user can set during registration. These attributes are based on the AM identity repository.
For Destination After Successful Registration, select one of the following options:
auto-login. User is automatically logged in and sent to the appropriate page within the system.
default. User is sent to a success page without being logged in. In this case, AM displays a "You have successfully registered" page. The user can then click the Login link to log in to AM. This is the default selection.
login. User is sent to the login page to authenticate.
Save your changes.
Under the Advanced Configuration tab, configure the User Registration Confirmation Email URL for your deployment. The default is:
https://openam.example.com:8443/openam/XUI/?realm=${realm}#register/.Save your changes.
Like AM, IDM offers user self-registration functionality. However, IDM provides additional onboarding and provisioning features.
You can delegate user registration to IDM after a user has authenticated to AM, using a social identity authentication module, for example.
For IDM to complete the registration process:
AM and IDM must be connected to the same user data store.
For more information, see shared identity store in the ForgeRock Identity Platform documentation.
AM and IDM must share the signing and encryption keys used for self-service.
You can supply your own keys for both servers, or you can use the default IDM keys.
To use the default IDM keys, follow the instructions in Copying Key Aliases to copy the following key aliases from the IDM keystore to the AM keystore:
openidm-selfservice-key—encrypts JWT self-service tokens using HS256 (HMAC with SHA-256) (SecretKeyEntry)selfservice—Signs JWT session tokens using RSA (PrivateKeyEntry)
When you have copied the keys, restart AM to apply the changes.
In the AM console, go to Configure > Global Services > IDM Provisioning.
Perform the following actions on the IDM Provisioning page:
Enable the IDM Provisioning service by selecting Enabled.
Enter the URL of the IDM instance in the Deployment URL field, for example
https://openidm.example.com.(Optional) If you created new signing or encryption keys, enter their details, ensuring the keys are identical and available in the default keystores of both AM and IDM.
For more information on IDM security, see the ForgeRock Identity Management 7.1 Security Guide.
If you used the default IDM keys, enter the following key information:
In the provisioningSigningKeyAlias field, enter
selfservice.In the provisioningEncryptionKeyAlias field, enter
openidm-selfservice-key.In the provisioningSigningAlgorithm field, enter
HS256.In the provisioningEncryptionAlgorithm field, enter
RSAES_PKCS1_V1_5.In the provisioningEncryptionMethod field, enter
A128CBC_HS256.
If you are using IDM 6 or earlier, enable the Signing Compatibility Mode property.
For details of the available properties, see "IDM Provisioning".
Save your changes.
In the AM console, go to Realms > Realm Name > Authentication > Modules, and create or select a social authentication module in which to enable IDM user registration.
On the social authentication module page, perform the following actions on the Account Provisioning tab:
Select Use IDM as Registration Service.
Ensure Create account if it does not exist is enabled.
Save your changes.
Successfully authenticating to a social authentication module that has IDM as the registration service redirects the user to IDM to complete the user registration.
For information on integrating AM and IDM, see the Platform Setup Guide.
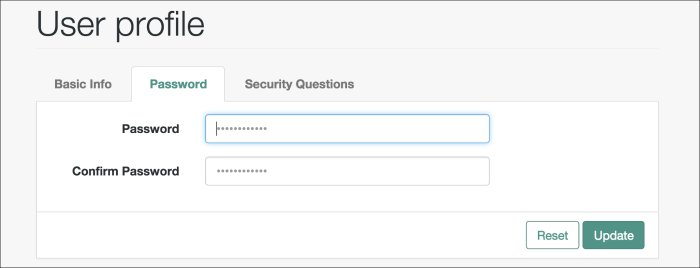
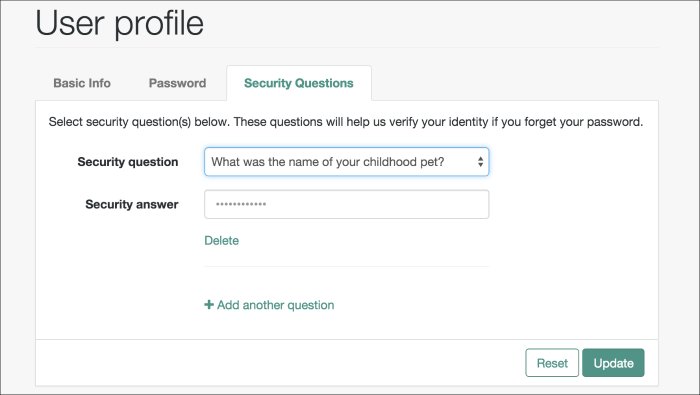
User Management of Passwords and Security Questions
Once the user has self-registered to your system, they can change their password and security questions at any time on the user profile page. The user profile page provides tabs to carry out these functions.