Combined MFA Registration node
The Combined MFA Registration node lets an authenticated user register a device, such as a mobile phone, for multi-factor authentication with a push notification and an OATH one-time password in a single step.
This node can make journeys less complex by combining the functionality of the Push Registration node and OATH Registration node.
The node displays a single QR code that users scan to register their device for both push and OATH authentication. Journeys can use the Push Sender node to verify possession of the registered device. If push doesn’t succeed, for example, if the user’s device doesn’t have internet access, the journey can fall back to the OATH Token Verifier node to request a one-time password using OATH.
Learn more about push notifications and OATH one-time passwords in MFA: Push authentication and MFA: OATH authentication.
Compatibility
| Product | Compatible? |
|---|---|
ForgeRock Identity Cloud |
|
ForgeRock Access Management (self-managed) |
|
ForgeRock Identity Platform (self-managed) |
Inputs
The node reads the username of the identity that is registering for MFA from the shared state. Implement a
Username Collector node (standalone AM) or Platform Username node (ForgeRock Identity Platform deployment)
before this node in the journey.
Dependencies
This node requires that you configure the Push Notification Service.
Learn more about provisioning the credentials required by the Push Notification Service in How To Configure Service Credentials (Push Auth, Docker) in Backstage in the ForgeRock Knowledge Base.
For detailed information about the available properties, refer to Push Notification Service.
Configuration
| Property | Usage | ||
|---|---|---|---|
Issuer |
An identifier to appear on the user’s device, such as a company name, a website, or a realm. The value is displayed by the authenticator application. For example, Default: |
||
Account Name |
The profile attribute to display as the username in the authenticator application. If not specified, or if the specified profile attribute is empty, the username is used. Default: |
||
Background Color |
The background color in hex notation that displays behind the issuer’s logo within the authenticator application. Default: |
||
Logo Image URL |
The location of an image to download and display as the issuer’s logo within the authenticator application.
Default: none |
||
Generate Recovery Codes |
If enabled, recovery codes are generated and stored in the successful outcome’s transient state. Use the Recovery Code Display node to display the codes to the user for safekeeping. Default: true
|
||
QR code message |
A custom, localized message with instructions to scan the QR code to register the device.
Default: none |
||
Registration Response Timeout |
The period of time (in seconds) to wait for a response to the registration QR code. If no response is received during
this time, evaluation continues along the Default: |
||
One Time Password Length |
The length of the generated OTP in digits. This value must be at least Default: |
||
Minimum Secret Key Length |
Minimum number of hexadecimal characters allowed for the Secret Key. Default: |
||
OATH Algorithm |
The algorithm the device uses to generate the OTP:
Default: |
||
TOTP Time Step Interval ( |
The length of time that an OTP is valid in seconds. For example, if the time step interval is 30 seconds, a new OTP is generated every 30 seconds and is valid for 30 seconds only. Default: |
||
TOTP Hash Algorithm |
The HMAC hash algorithm used to generate the OTP codes. AM supports SHA1, SHA256, and SHA512. Default: |
||
HOTP Checksum Digit |
Add a digit to the end of the generated OTP to be used as a checksum to verify the OTP was generated correctly. This is in addition to the actual password length. Only set this if the user devices support it. Default: false |
||
HOTP Truncation Offset |
An option used by the HOTP algorithm that not all devices support. Leave the default value unless you know user devices use an offset. Default: |
||
JSON Authenticator Policies |
Policies to apply to the device being registered, in JSON format. Use the following format to apply policies: json Supported policies The ForgeRock Authenticator app supports enforcement of the following default policies:
Example: json |
Outcomes
- Success
-
Device registration succeeded.
- Failure
-
AM encountered an issue when attempting to register the authentication device.
- Time Out
-
The node didn’t receive a response from the device within the time specified in the configuration.
Outputs
-
For Push registration, this node updates the shared state with the push device settings, the message ID and the push challenge.
-
For OATH registration, this node records the device profile in the
oathDeviceProfileshared state attribute and the recovery codes in theoathEnableRecoveryCodeshared state attribute.
Errors
- No username found
-
The node failed to read the username from the shared state.
- Unable to find push message ID in sharedState
-
The node failed to read the push message ID from the shared state.
Example
The following example shows an implementation of combined multi-factor registration in an authentication journey:
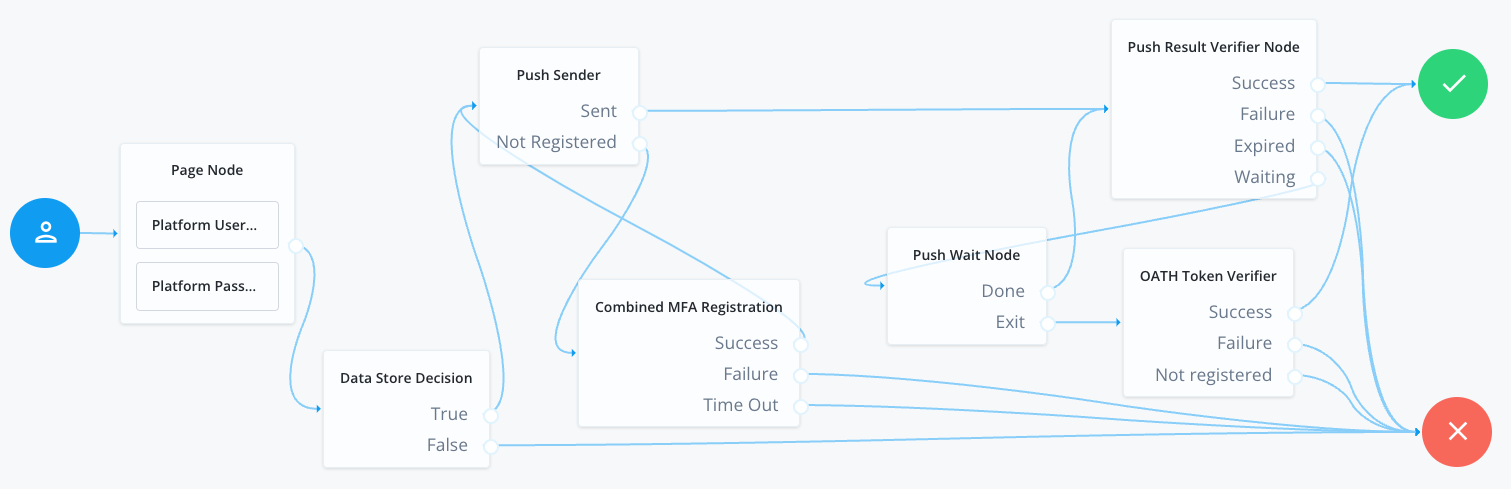
-
The Page node with the Platform Username node and the Platform Password node prompts for the user credentials.
-
The Data Store Decision node confirms the username-password credentials.
-
The Push Sender node determines whether the user has a registered device.
-
If the user has a registered device:
-
The Push Sender node sends a push notification to the device.
-
The Push Result Verifier node validate the user’s response to the push notification, looping through the Push Wait node until authentication succeeds.
-
The Push Wait node lets the user cancel the wait for a push notification. In this case evaluation continues to the OATH Token Verifier node, so the user can enter a one-time password instead.
-
-
If the user doesn’t have a registered device:
-
The Push Sender node routes the user to the Combined MFA Registration node, which displays a QR code to the user to register a device.
After successful registration of a device for both push and OATH authentication, evaluation returns to the Push Sender node and continues with the registered device.
-
-