Authorization Code Grant with PKCE
The Authorization Code grant, when combined with the PKCE standard (RFC 7636), is used when the client, usually a mobile or a JavaScript application, requires access to protected resources.
The flow is similar to the regular Authorization Code grant type, but the client must generate a code that will be part of the communication between the client and the authorization server. This code mitigates against interception attacks performed by malicious users.
Since communication between the client and the authorization server is not secure, clients are usually public so their secrets do not get compromised. Also, browser-based clients making OAuth 2.0 requests to different domains must implement Cross-Origin Resource Sharing (CORS) calls to access OAuth 2.0 resources in different domains.
The PKCE flow adds three parameters on top of those used for the Authorization code grant:
code_verifier (form parameter). Contains a random string that correlates the authorization request to the token request.
code_challenge (query parameter). Contains a string derived from the code verifier that is sent in the authorization request and that needs to be verified later with the code verifier.
code_challenge_method (query parameter). Contains the method used to derive the code challenge.
The steps in the diagram are described below:
The client receives a request to access a protected resource. To access the resources, the client requires authorization from the resource owner. When using the PKCE standard, the client must generate a unique code and a way to verify it, and append the code to the request for the authorization code.
The client redirects the resource owner's user-agent to the authorization server.
The authorization server authenticates the resource owner, confirms resource access, and gathers consent if not previously saved.
If the resource owner's credentials are valid, the authorization server stores the code challenge and redirects the resource owner's user agent to the redirection URI.
During the redirection process, the authorization server appends an authorization code to the request to the client.
The client receives the authorization code and calls the authorization server's token endpoint to exchange the authorization code for an access token appending the verification code to the request.
The authorization server verifies the code stored in memory using the validation code. It also verifies the authorization code. If both codes are valid, the authorization server returns an access token (and a refresh token, if configured) to the client.
The client requests access to the protected resources from the resource server.
The resource server contacts the authorization server to validate the access token.
The authorization server validates the token and responds to the resource server.
If the token is valid, the resource server allows the client to access the protected resources.
Perform the steps in the following procedures to obtain an authorization code and exchange it for an access token:
The client application must be able to generate a code verifier and a code challenge. For details, see the PKCE standard (RFC 7636). The information contained in this procedure is for example purposes only:
The client generates the code challenge and the code verifier. Creating the challenge using a SHA-256 algorithm is mandatory if the client supports it, as per the RFC 7636 standard.
The following is an example of a code verifier and code challenge written in JavaScript:
function base64URLEncode(words) { return CryptoJS.enc.Base64.stringify(words) .replace(/\+/g, '-') .replace(/\//g, '_') .replace(/=/g, ''); } var verifier = base64URLEncode(CryptoJS.lib.WordArray.random(50)); var challenge = base64URLEncode(CryptoJS.SHA256(verifier));This example generates values such as
ZpJiIM_G0SE9WlxzS69Cq0mQh8uyFaeEbILlW8tHs62SmEE6n7Nke0XJGx_F4OduTI4for the code verifier andj3wKnK2Fa_mc2tgdqa6GtUfCYjdWSA5S23JKTTtPF8Yfor the code challenge. These values will be used in subsequent procedures.The client is now ready to request an authorization code.
The client performs the steps in one of the following procedures to request an authorization code:
This procedure assumes the following configuration:
AM is configured as an OAuth 2.0 authorization server. Ensure that:
The
codeplugin is configured in the Response Type Plugins field.The
Authorization Codegrant type is configured in the Grant Types field.
The Code Verifier Parameter Required drop-down (Realms > Realm Name > Services > OAuth2 Provider > Advanced) specifies whether AM require clients to include a code verifier in their calls.
However, if a client makes a call to AM with the
code_challengeparameter, AM will honor the code exchange regardless of the configuration of the Code Verifier Parameter Required drop-down.A public client called
myClientis registered in AM with the following configuration:Scopes:
writeResponse Types:
codeGrant Types:
Authorization Code
For more information, see Client Registration.
Perform the steps in this procedure to obtain an authorization code using a browser:
The client redirects the resource owner's user-agent to the authorization server's authorization endpoint specifying, at least, the following query parameters:
client_id=your_client_id
response_type=code
redirect_uri=your_redirect_uri
code_challenge=your_code_challenge
code_challenge_method=S256
For information about the parameters supported by the
/oauth2/authorizeendpoint, see "/oauth2/authorize".If the OAuth 2.0 provider is configured for a subrealm rather than the Top Level Realm, you must specify it in the endpoint. For example, if the OAuth 2.0 provider is configured for the
/alpharealm, then use/oauth2/realms/root/realms/alpha/authorize.For example:
https://openam.example.com:8443/openam/oauth2/realms/root/realms/alpha/authorize \ ?client_id=myClient \ &response_type=code \ &scope=write \ &redirect_uri=https://www.example.com:443/callback \ &code_challenge=j3wKnK2Fa_mc2tgdqa6GtUfCYjdWSA5S23JKTTtPF8Y \ &code_challenge_method=S256 \ &state=abc123
Note that the URL is split and spaces have been added for readability purposes and that the
scopeandstateparameters have been included. Scopes are not required, since they can be configured by default in the authorization server and the client, and have been added only as an example. Thestateparameter is added to protect against CSRF attacks.The resource owner authenticates to the authorization server, for example, using the credentials of the
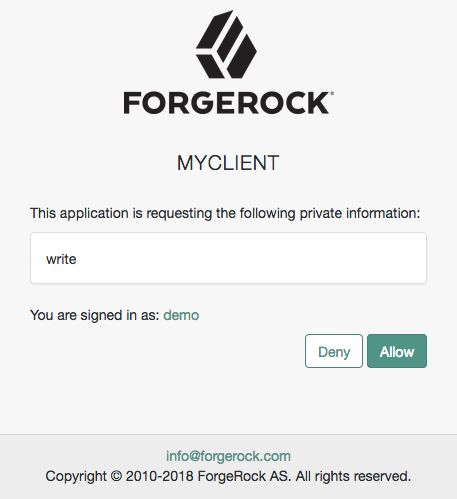
demouser. In this case, they log in using the default chain or tree configured for the realm.After logging in, the authorization server presents the AM consent screen:
The resource owner selects the
Allowbutton to grant consent for thewritescope.The authorization server redirects the resource owner to the URL specified in the
redirect_uriparameter.Inspect the URL in the browser. It contains a
codeparameter with the authorization code the authorization server has issued. For example:http://www.example.com/?code=ZNSDo8LrsI2w-6NOCYKQgvDPqtg&scope=write&iss=https%3A%2F%2Fopenam.example.com%3A8443%2Fopenam%2Foauth2&state=abc123&client_id=myClient
The client performs the steps in "To Exchange an Authorization Code for an Access Token" to exchange the authorization code for an access token.
This procedure assumes the following configuration:
AM is configured as an OAuth 2.0 authorization server. Ensure that:
The
codeplugin is configured in the Response Type Plugins field.The
Authorization Codegrant type is configured in the Grant Types field.
The Code Verifier Parameter Required drop-down (Realms > Realm Name > Services > OAuth2 Provider > Advanced) specifies whether AM require clients to include a code verifier in their calls.
However, if a client makes a call to AM with the
code_challengeparameter, AM will honor the code exchange regardless of the configuration of the Code Verifier Parameter Required drop-down.A public client called
myClientis registered in AM with the following configuration:Scopes:
writeResponse Types:
codeGrant Types:
Authorization Code
For more information, see Client Registration.
Perform the steps in this procedure to obtain an authorization code:
The resource owner logs in to the authorization server, for example, using the credentials of the
demouser. For example:$
curl \ --request POST \ --header "Content-Type: application/json" \ --header "X-OpenAM-Username: demo" \ --header "X-OpenAM-Password: Ch4ng31t" \ --header "Accept-API-Version: resource=2.0, protocol=1.0" \ 'https://openam.example.com:8443/openam/json/realms/root/realms/alpha/authenticate'{ "tokenId":"AQIC5wM...TU3OQ*", "successUrl":"/openam/console", "realm":"/alpha" }The client makes a POST call to the authorization server's authorization endpoint specifying in a cookie SSO token of the
demoand, at least, the following parameters:client_id=your_client_id
response_type=code
redirect_uri=your_redirect_uri
decision=allow
csrf=demo_user_SSO_token
code_challenge=your_code_challenge
code_challenge_method=S256
For information about the parameters supported by the
/oauth2/authorizeendpoint, see "/oauth2/authorize".If the OAuth 2.0 provider is configured for a subrealm rather than the Top Level Realm, you must specify it in the endpoint. For example, if the OAuth 2.0 provider is configured for the
/alpharealm, then use/oauth2/realms/root/realms/alpha/authorize.For example:
$
curl --dump-header - \ --request POST \ --Cookie "iPlanetDirectoryPro=AQIC5wM...TU3OQ*" \ --data "redirect_uri=https://www.example.com:443/callback" \ --data "scope=write" \ --data "response_type=code" \ --data "client_id=myClient" \ --data "csrf=AQIC5wM...TU3OQ*" \ --data "state=abc123" \ --data "decision=allow" \ --data "code_challenge=j3wKnK2Fa_mc2tgdqa6GtUfCYjdWSA5S23JKTTtPF8Y" \ --data "code_challenge_method=S256" \ "https://openam.example.com:8443/openam/oauth2/realms/root/realms/alpha/authorize"Note that the
scopeand thestateparameters have been included. Scopes are not required, since they can be configured by default in the authorization server and the client, and have been added only as an example. Thestateparameter is added to protect against CSRF attacks.If the authorization server is able to authenticate the user and the client, it returns an HTTP 302 response with the authorization code appended to the redirection URL:
HTTP/1.1 302 Found Server: Apache-Coyote/1.1 X-Frame-Options: SAMEORIGIN Pragma: no-cache Cache-Control: no-store Date: Mon, 30 Jul 2018 11:42:37 GMT Accept-Ranges: bytes Location: http://www.example.com?code=g5B3qZ8rWzKIU2xodV_kkSIk0F4&scope=write&iss=https%3A%2F%2Fopenam.example.com%3A8443%2Fopenam%2Foauth2&state=abc123&client_id=myClient Vary: Accept-Charset, Accept-Encoding, Accept-Language, Accept Content-Length: 0Perform the steps in "To Exchange an Authorization Code for an Access Token in the Authorization Code Grant Flow with PKCE Flow" to exchange the authorization code for an access token.
Perform the steps in the following procedure to exchange an authorization code for an access token:
Ensure the client has obtained an authorization code by performing the steps in either "To Obtain an Authorization Code Using a Browser in the Authorization Code Grant with PKCE Flow" or "To Obtain an Authorization Code Without Using a Browser in the Authorization Code Grant with PKCE Flow".
The client creates a POST request to the token endpoint in the authorization server specifying, at least, the following parameters:
grant_type=authorization_code
code=your_authorization_code
client_id=your_client_id
redirect_uri=your_redirect_uri
code_verifier=your_code_verifier
For information about the parameters supported by the
/oauth2/access_tokenendpoint, see "/oauth2/access_token". For information about private client authentication methods, see OAuth 2.0 Client Authentication.For example:
$
curl --request POST \ --data "grant_type=authorization_code" \ --data "code=g5B3qZ8rWzKIU2xodV_kkSIk0F4" \ --data "client_id=myClient" \ --data "redirect_uri=https://www.example.com:443/callback" \ --data "code_verifier=ZpJiIM_G0SE9WlxzS69Cq0mQh8uyFaeEbILlW8tHs62SmEE6n7Nke0XJGx_F4OduTI4" \ "https://openam.example.com:8443/openam/oauth2/realms/root/realms/alpha/access_token"The
client_idand theredirection_uriparameters specified in this call must match those used as part of the authorization code request, or the authorization server will not validate the code.The authorization server returns an access token in the
access_tokenproperty. For example:{ "access_token": "sbQZuveFumUDV5R1vVBl6QAGNB8", "scope": "write", "token_type": "Bearer", "expires_in": 3599 }Tip
The authorization server can also issue refresh tokens at the same time the access tokens are issued. For more information, see Refresh Tokens.