Install IIS and ISAPI Web Agents Documentation
IIS and ISAPI Web Agents Documentation instances can be configured to operate with multiple websites. Each configuration instance is independent and has its own configuration file, debug logs, and audit logs. Each instance can connect to a different AM realm, or even different AM servers.
Consider the following points for IIS and ISAPI Web Agents Documentation:
-
IIS agents must run in Integrated mode.
-
IIS and ISAPI agents can’t run in the same Windows Server instance.
-
ISAPI agent handles the POST method for form data but not for other data types.
-
An agent configured for a site or parent application protects any application configured in the site or parent application.
-
A protected application configured for a site or parent application protects any application configured in the site or parent application.
-
Agents configured in a site or parent application protect only the child applications that inherit their parent IIS or ISAPI configuration.
-
Because of architectural differences, agents configured for a site or parent application running in a 64-bit pool don’t protect child applications running in a 32-bit pool. 32-bit applications can’t load 64-bit web agent libraries.
Similarly, agents configured for a site or parent application running in a 32-bit pool don’t protect child applications running in a 64-bit pool.
In this case, child applications require their own agent installation, as explained in the next item of this list. Both 32-bit and 64-bit agent libraries are supplied with the IIS and ISAPI Web Agents Documentation binaries.
-
If an application requires a specific agent configuration or, for example, the application is a 32-bit application configured within a 64-bit site, follow the procedures in this section to create a new agent instance for it. Configuring an agent on an application overrides the application’s parent web agent configuration, if any.
Install Web Agents Documentation on the child application before installing it in the parent. Trying to install an agent on a child that is already protected causes an error. -
(For IIS agent) You can disable the agent protection at any level of the IIS hierarchy, with the following constraints:
-
Disabling the agent in a parent application disables protection on all child applications that don’t have a specific agent instance installed on them.
-
Disabling the agent in a child application doesn’t disable protection on its parent application.
-
-
(For ISAPI agent) You can’t disable the agent protection. ISAPI agent is either installed and running or not installed.
-
Agents require that the Application Development component is installed alongside the core IIS or ISAPI services. Application Development is an optional component of the IIS and ISAPI web server. The component provides required infrastructure for hosting web applications.
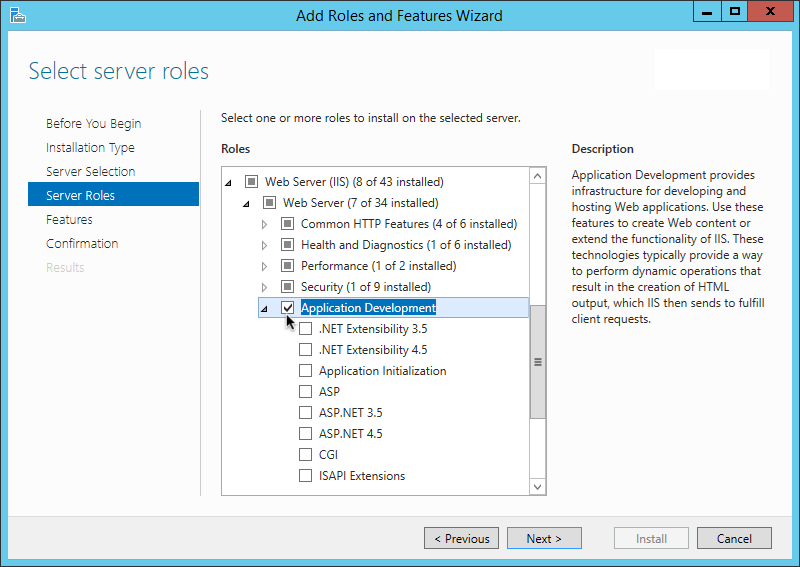 Figure 1. Adding the application development component to IIS and ISAPI
Figure 1. Adding the application development component to IIS and ISAPI -
The following properties don’t work with ISAPI agent:
Install IIS or ISAPI Web Agents Documentation interactively
-
Review the information in Before you install, and perform the steps in Preinstallation tasks.
-
Log on to Windows as a user with administrator privileges.
-
Make sure AM is running.
-
Run the agentadmin --i command to install the agent.
c:\> cd web_agents\iis_agent\bin c:\web_agents\iis_agent\bin> agentadmin.exe --i
-
When prompted, enter information for your deployment.
To cancel the installation at any time, press CTRL-C.-
Choose the site and application in which to install the web agent.
The
agentadmincommand reads the IIS or ISAPI server configuration and converts hierarchy as follows:-
(For ISAPI agent) Into a single value ID.
-
(For IIS agent) Into an ID composed of three values separated by the dot (
.) character:The first value specifies an IIS site. The number
1specifies the first site in the server.The second value specifies an application configured in an IIS site. The number
1specifies the first application in the site.The third value specifies an internal value for the web agent.
The following is an example IIS server configuration read by the
agentadmincommand:IIS Server Site configuration: ==================================== id details ==================================== Default Web Site application path:/, pool DefaultAppPool 1.1.1 virtualDirectory path:/, configuration: C:\inetpub\wwwroot\web.config MySite application path:/, pool: MySite 2.1.1 virtualDirectory path:/, configuration C:\inetpub\MySite\web.config application path:/MyApp1, pool: MySite 2.2.1 virtualDirectory path:/ configuration C:\inetpub\MySite\MyApp1\web.config application path:/MyApp1/MyApp2, pool: MySite 2.3.1 virtualDirectory path:/ configuration C:\inetpub\MySite\MyApp1\MyApp2\web.config Enter IIS Server Site identification number. [ q or 'ctrl+c' to exit ] Site id: 2.1.1-
ID
2.1.1corresponds to the first application,/configured in a second IIS site,MySite. You would choose this ID to install the web agent at the root of the site. -
ID
2.2.1corresponds to a second application,MyApp1, configured in a second IIS site,MySite. You would choose this ID to install the web agent in theMyApp1application. -
ID
2.3.1corresponds to a child application,MyApp1/MyApp2, configured in the second application,MyApp1, configured in a second IIS site,MySite. You would choose this ID to install the web agent in the sub-application,MyApp1/MyApp2.
-
-
-
The installer can import settings from an existing web agent on the new installation and skips prompts for any values present in the existing configuration file. You will be required to re-enter the agent profile password.
Enter the full path to an existing agent configuration file to import the settings, or press
Enterto skip the import.To set properties from an existing configuration enter path to file [ q or 'ctrl+c' to exit, return to ignore ] Existing agent.conf file:
-
Enter the full URL of the AM instance the agent will use. Ensure the deployment URI is specified.
If a reverse proxy is configured between AM and the agent, set the AM URL to the proxy URL, for example, https://proxy.example.com:443/am. For information about setting up an environment for reverse proxies, refer to Apache as a reverse proxy.Enter the URL where the AM server is running. Please include the deployment URI also as shown below: (http://am.sample.com:58080/am) [ q or 'ctrl+c' to exit ] AM server URL: https://am.example.com:8443/am
-
Enter the full URL of the site the agent will run in.
Enter the Agent URL as shown below: (http://agent.sample.com:1234) [ q or 'ctrl+c' to exit ] Agent URL: http://customers.example.com:80
-
Enter the name given to the agent profile created in AM.
Enter the Agent profile name [ q or 'ctrl+c' to exit ] Agent Profile name: iisagent
-
Enter the agent profile realm. Realms are case-sensitive.
Enter the Agent realm/organization [ q or 'ctrl+c' to exit ] Agent realm/organization name: [/]: /
-
Enter the full path to the file containing the agent profile password created earlier.
Enter the path to a file that contains the password to be used for identifying the Agent [ q or 'ctrl+c' to exit ] The path to the password file: c:\pwd.txt
-
The installer displays a summary of the configuration settings you specified.
If a setting is incorrect, type
no, or pressEnter. The installer loops through the configuration prompts using your provided settings as the default. PressEnterto accept each one, or enter a replacement setting.If the settings are correct, type
yesto proceed with installation.Installation parameters: AM URL: https://am.example.com:8443/am Agent URL: http://customers.example.com:80 Agent Profile name: iisagent Agent realm/organization name: / Agent Profile password source: c:\pwd.txt Confirm configuration (yes/no): [no]: yes Validating… Validating… Success. Cleaning up validation data… Creating configuration… Installation complete.
On successful completion, the installer adds the agent as a module to the IIS or ISAPI site configuration.
To ease logging, the installer grants full user access permissions on the IIS or ISAPI instance folder. Each agent instance has a numbered configuration and logs directory.
-
For IIS, the first agent configuration and logs are located in
web_agents\iis_agent\instances\agent_1\. -
For ISAPI, the agent ID corresponds to the site ID. If site 5 is used, the agent configuration and logs are located in
web_agents\iis_agent\instances\agent_5\.
-
-
-
Ensure the application pool identity related to the IIS site has the appropriate permissions on the following agent installation folders:
-
\web_agents\iis_agent\lib -
\web_agents\iis_agent\log -
\web_agents\iis_agent\instances\agent_nnnTo change the ACLs for files and folders related to the agent instance, run the
agentadmin --ocommand. For example:C:\web_agents\iis_agent\bin>agentadmin.exe --o "ApplicationPoolIdentity1" "C:\web_agents\iis_agent\lib"
Learn more from agentadmin command.
When permissions are not set correctly, errors such as getting a blank page when accessing a protected resource can occur.
-
-
If you installed Web Agents Documentation in an application, set CDSSO Redirect URI to the application path, as follows:
-
Go to Realms > Realm Name > Agents > Web > Agent Name > SSO > Cross Domain SSO.
-
Add the application path to the default value of CDSSO Redirect URI. For example, if you installed Web Agents Documentation in an application such as
MyApp1/MyApp2, set the property toMyApp1/MyApp2/agent/cdsso-oauth2. -
Save your changes.
-
Install IIS or ISAPI Web Agents Documentation silently
-
Review the information in Before you install, and perform the steps in Preinstallation tasks.
-
Make sure AM is running.
-
Run the agentadmin --s command with the required arguments. For example:
c:\web_agents\iis_agent\bin> agentadmin.exe --s ^ "2.1.1" ^ "https://am.example.com:8443/am" ^ "http://iis.example.com:80" ^ "/" ^ "iisagent" ^ "c:\pwd.txt" ^ AM Web Agents Documentation for IIS Server installation. Validating… Validating… Success. Cleaning up validation data… Creating configuration… Installation complete.
-
Ensure the application pool identity related to the IIS site has the appropriate permissions on the following agent installation folders:
-
\web_agents\iis_agent\lib -
\web_agents\iis_agent\log -
\web_agents\iis_agent\instances\agent_nnnTo change the ACLs for files and folders related to the agent instance, run the
agentadmin --ocommand. For example:C:\web_agents\iis_agent\bin>agentadmin.exe --o "ApplicationPoolIdentity1" "C:\web_agents\iis_agent\lib"
Learn more from agentadmin command.
When permissions are not set correctly, errors such as getting a blank page when accessing a protected resource can occur.
-
-
(Optional) If you installed the agent in a parent application, enable it for its child applications, as described in Disable and enable agent protection for child applications.
Enable and disable IIS Web Agents Documentation
| ISAPI Web Agents Documentation can’t be enabled or disabled; it is either installed and running or not installed. |
Disable and enable Web Agents Documentation on an IIS site or application
The agentadmin command shows only instances of the agent. Learn about how to
enable or disable the protection of child applications in
Disable and enable agent protection for child applications.
-
Log on to Windows as a user with administrator privileges.
-
Run the agentadmin --l command to list the installed agent configuration instances.
c:\web_agents\iis_agent\bin> agentadmin.exe --l AM Web Agents Documentation configuration instances: id: agent_1 configuration: c:\web_agents\iis_agent\bin\..\instances\agent_1 server/site: 2.2.1
Make a note of the ID value of the configuration instance you want to disable or enable.
-
Perform one of the following steps:
-
To disable the agent in a site, run the agentadmin --d command and specify the ID of the agent configuration instance to disable.
c:\web_agents\iis_agent\bin> agentadmin.exe --d agent_1 Disabling agent_1 configuration… Disabling agent_1 configuration… Done.
-
To enable the agent in a site, run the agentadmin --e command and specify the ID of the agent configuration instance to enable.
c:\web_agents\iis_agent\bin> agentadmin.exe --e agent_1 Enabling agent_1 configuration… Enabling agent_1 configuration… Done.
-
Disable and enable agent protection for child applications
-
Edit the child application’s
web.configconfiguration. -
Decide whether to enable or disable agent protection:
-
To disable agent protection, add the following lines to the child application’s
web.configfile:<OpenAmModule enabled="false" configFile="C:\web_agents\iis_agent\instances\agent_1\config\agent.conf" /> <modules> <add name="OpenAmModule64" preCondition="bitness64" /> </modules>Note that the path specified in
configFilemay be different for your environment. -
To enable agent protection, understand that agents configured in a site or parent application also protect any applications that inherit the IIS configuration from that site or parent.
If you have disabled the agent’s protection for a child application by following the steps in this procedure, remove the lines added to the
web.configfile to enable protection again.
-
Enable support for basic authentication and password replay
| ISAPI Web Agents Documentation doesn’t support password replay. |
The IIS Web Agents Documentation supports basic authentication and password replay. Use the appropriate software versions.
Given the proper configuration and with Active Directory as a user data store for AM, the IIS agent can provide access to IIS server variables. The instructions for configuring the capability follow in this section, though you should read the section in full, also paying attention to the required workarounds for Microsoft issues.
When configured as described, the agent requests IIS server variable values from AM, which gets them from Active Directory. The agent then sets the values in HTTP headers so that they can be accessed by your application.
The following IIS server variables all take the same value when set:
REMOTE_USER, AUTH_USER, and login_USER. The agent either sets all
three, or doesn’t set any of them.
When Logon and Impersonation is enabled, the agent performs Windows login and sets the user impersonation token in the agent session context.
When
Show Password in HTTP Header
is enabled, the agent adds the password in the USER_PASSWORD header.
The agent doesn’t modify any other IIS server variables related to the authenticated user’s session.
The agent requires that IIS runs in Integrated mode. Consider the following points for integration with additional Microsoft products:
-
For Microsoft Office integration, use Microsoft Office 2007 SP2 or later.
-
For Microsoft SharePoint integration, use Microsoft SharePoint Server 2007 SP2 or later.
Microsoft issues
Apply workarounds for the following Microsoft issues:
- Microsoft support issue: 841215
-
Link: http://support.microsoft.com/kb/841215
Description: Error message when you try to connect to a Windows SharePoint document library: "System error 5 has occurred".
Summary: Enable Basic Authentication on the client computer.
- Microsoft support issue: 870853
-
Link: http://support.microsoft.com/kb/870853
Description: Office 2003 and 2007 Office documents open read-only in Internet Explorer.
Summary: Add registry keys as described in Microsoft’s support document.
- Microsoft support issue: 928692
-
Link: http://support.microsoft.com/kb/928692
Description: Error message when you open a Web site by using Basic authentication in Expression Web on a computer that is running Windows Vista: "The folder name isn’t valid".
Summary: Edit the registry as described in Microsoft’s support document.
- Microsoft support issue: 932118
-
Link: http://support.microsoft.com/kb/932118
Description: Persistent cookies are not shared between Internet Explorer and Office applications.
Summary: Add the website the list of trusted sites.
- Microsoft support issue: 943280
-
Link: http://support.microsoft.com/kb/943280
Description: Prompt for Credentials When Accessing FQDN Sites From a Windows Vista or Windows 7 Computer.
Summary: Edit the registry as described in Microsoft’s support document.
- Microsoft support issue: 968851
-
Link: http://support.microsoft.com/kb/968851
Description: SharePoint Server 2007 Cumulative Update Server Hotfix Package (MOSS server-package): April 30, 2009.
Summary: Apply the fix from Microsoft if you use SharePoint.
- Microsoft support issue: 2123563
-
Link: http://support.microsoft.com/kb/2123563
Description: You cannot open Office file types directly from a server that supports only Basic authentication over a non-TLS connection.
Summary: Enable TLS communications on the web server.
To Configure basic authentication and password replay support
-
Use the
openssltool to generate a suitable encryption key:$ openssl rand -base64 32 e63…sw=
-
In the AM admin UI, go to Deployment > Servers > Server Name > Advanced, and then add a property
com.sun.am.replaypasswd.keywith the encryption key you generated in a previous step as the value. -
Go to Realms > Realm Name > Authentication > Settings > Post Authentication Processing, and in Authentication Post Processing Classes, add the class
com.sun.identity.authentication.spi.ReplayPasswd. -
Restart AM.
-
In the AM admin UI go to Realms > Realm Name > Applications > Agents > Web > Agent Name > Advanced
-
(AM 7.4.x and earlier versions) In Replay Password Key, enter the encryption key generated in a previous step. The field corresponds to Replay Password Key.
From AM 7.5, setting this property in the AM admin UI is deprecated. Values set in this field of the AM admin UI are ignored. The value of the DES key is inherited from the secret mapped to the AM secret label am.authentication.replaypassword.key. -
For Windows login for user token impersonation, enable Logon and Impersonation.
-
Save your changes.
-
-
(Optional) To set the encrypted password in the IIS
AUTH_PASSWORDserver variable, go to Realms > Realm Name > Applications > Agents > Web > Agent Name > Advanced, and enable Show Password in HTTP Header. -
(Optional) If you require Windows login, or you need to use basic authentication with SharePoint or OWA, then you must do the following so that the agent requests AM to provide the appropriate account information from Active Directory in its policy response:
-
Configure Active Directory as a user data store
-
Configure the IIS or ISAPI agent profile User ID Parameter and User ID Parameter Type.
Skip this step if you don’t use SharePoint or OWA and no Windows login is required.
Make sure the AM data store is configured to use Active Directory as the user data store.
In the AM admin UI under Realms > Realm Name > Applications > Agents > Web > Agent Name > AM Services, set User ID Parameter and User ID Parameter Type.
For example, if the real username for Windows domain login in Active Directory is stored on the
sAMAccountNameattribute, then set the User ID Parameter tosAMAccountName, and the User ID Parameter Type toLDAP.Setting User ID Parameter Type to
LDAPcauses the web agent to request that AM get the value of the User ID Parameter attribute from the data store, in this case, Active Directory. Given that information, the agent can set the HTTP headersREMOTE_USER,AUTH_USER, orlogin_USERandUSER_PASSWORDwith Active Directory attribute values suitable for Windows login, setting the remote user, and so forth.
-
-
(Optional) To access Microsoft Office from SharePoint pages, configure AM to persist the authentication cookie. For information, refer to "Persistent cookie module" or "Persistent cookie decision node in AM’s Authentication and SSO guide.
Install in a subrealm
Examples in this document install the agent in the top-level realm. To install the agent in a subrealm during interactive or silent installation, use the subrealm during the installation or in the response file.
For example, instead of:
Agent realm/organization name: [/]: /specify:
Agent realm/organization name: [/]: /myrealmEven though the agent is installed in a subrealm, the default login redirect requires the user realm to be the top-level realm. For information about how to change the user realm, refer to Login redirect.