Deployment overview
These instructions show two sample deployments:
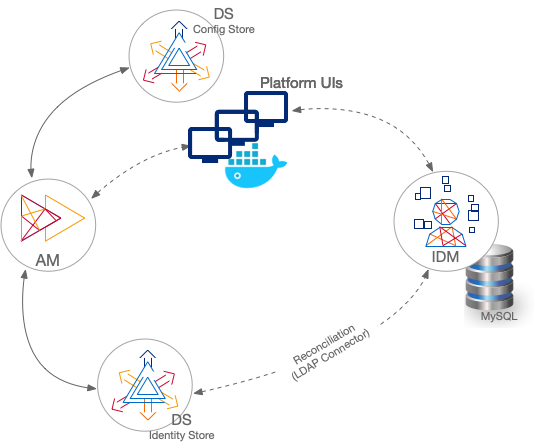
Separate identity stores
This deployment has an external DS instance configured as the AM configuration store, and a second external DS instance configured as the AM identity store. The IDM repository is an external JDBC database. The sample was tested with MySQL. The deployment uses an LDAP connector to synchronize the identities between IDM and AM:
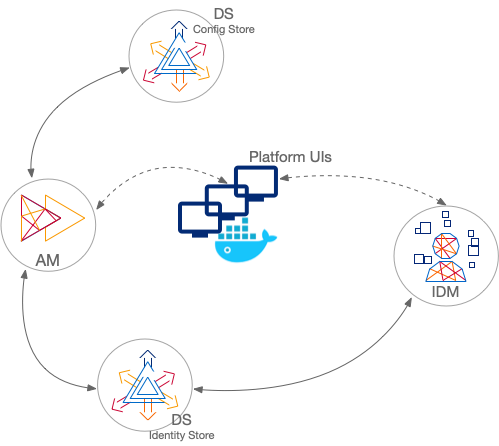
Shared Identity Store
This deployment has an external DS instance configured as the AM configuration store. The AM and IDM servers share an external DS instance as the identity store, and no synchronization configuration is required:
|
In both deployments, the Platform UIs can run in separate Docker containers. If you want to run the Platform UIs in containers, get Docker before you start. |
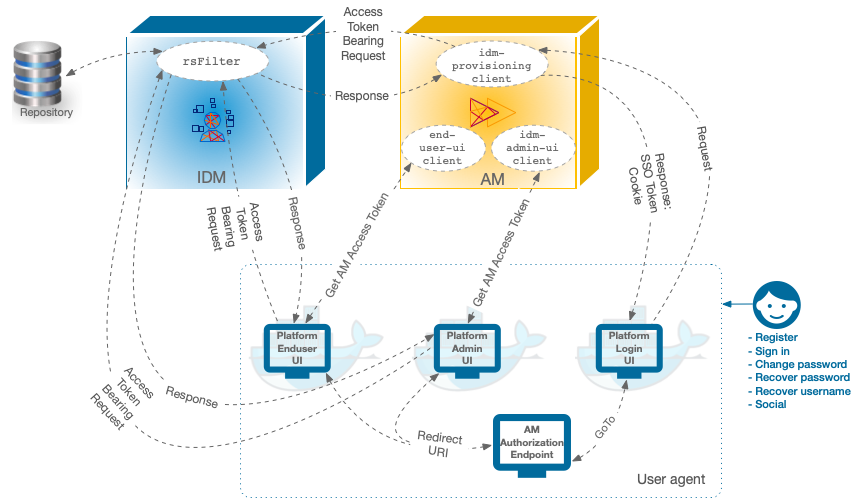
Component interaction
A platform configuration relies on multiple components working together.
The following image shows how the AM OAuth 2 clients interact
with the IDM resource server filter (rsFilter) to grant access through the Platform UIs:
-
The Platform UIs send a request to the AM Authorization Endpoint.
-
If the end user is authenticated, the user agent is redirected back to the UI, according to the Redirection URI request parameter.
-
If the end user is not authenticated, the AM Authorization Endpoint redirects the user agent to the Platform Login UI.
-
After successful authentication, the Platform Login UI redirects the user agent back to the AM Authorization Endpoint, according to the GoTo request parameter.
|
Server settings
These instructions assume that all servers are deployed on their own hosts, with the following server settings. Adjust the settings to match your own deployment.
|
To deploy the entire platform on a single computer, the recommended alternative is to use the ForgeOps Cloud Developer’s Kit (CDK) on Minikube. If you nevertheless choose to demonstrate these deployments on your computer,
add aliases for the fully qualified domain names used for AM, IDM and platform UIs
to your none Also, use a single DS server with all applicable DS setup profiles for your deployment.
You can use |
-
AM host:
am.example.com -
AM port:
8081 -
External DS configuration store host:
config.example.com -
External DS configuration store ports:
adminConnectorPort 4444
ldapPort 1389
ldapsPort 1636 -
External DS identity store host:
identities.example.comThese settings apply to both the separate and shared DS identity stores.
-
External DS identity store ports:
adminConnectorPort 4444
ldapPort 1389
ldapsPort 1636 -
IDM host:
openidm.example.com -
IDM ports:
HTTP 8080,HTTPS 8443 -
Platform Admin UI:
http://admin.example.com:8082 -
Platform Login UI:
http://login.example.com:8083 -
Platform End User UI:
http://enduser.example.com:8888