OAuth 2.0 scopes
OAuth 2.0 flows require scopes to limit the client’s access to the resource owner’s resources.
What are scopes?
Scopes are a way to restrict client access to the resource owner’s resources, as defined in the OAuth 2.0 Authorization Framework.
Scopes are not associated with data and, in practice, they are just concepts specified as strings that the resource server must interpret in order to provide the required access or resources to the client. The OAuth 2.0 framework does not define any particular value for scopes since they are dependent on the architecture of your environment.
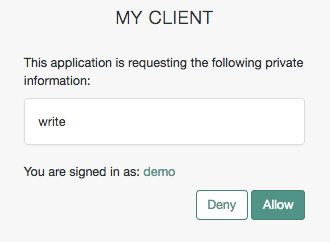
For example, a client may request the write scope,
which the resource server may interpret as that the client wants to save some new information in the user’s account,
such as images or documents.
A client can request one or more scopes, which AM may display in the consent screen. If the resource owner agrees to share access to their resources, scopes are included in the access token.
For security reasons, AM only accepts the scopes set in the Scope(s) or Default Scope(s) fields in the client profile (Realms > Realm Name > Applications > OAuth 2.0 > Clients > Client ID > Core).
If the client requests scopes, AM checks them against the Scope(s) field in the client profile.
If the client requests a scope that is not configured, AM returns an Unknown/invalid scope(s) error.
If the client does not request any scopes, AM uses the scopes in the Default Scope(s) field of the client profile. If no default scopes are set in the client profile, AM uses the scopes set in the Default Scope(s) field of the OAuth 2.0 provider.
If no scopes are configured by default, AM returns a No scope requested error.
AM does not use the default scopes in any other circumstance.
| You can use an access token modification script to override the allowed scopes specified at the OAuth 2.0 client level. |
The Client Registration Scope Allowlist field of the OAuth 2.0 provider restricts the scopes with which a client can register. In this sense, this field is used for OpenID Connect discovery and dynamic client registration only.
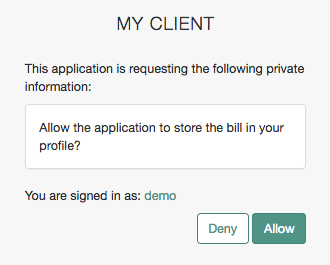
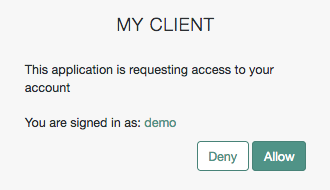
You can also use this field to configure how AM presents the scopes on the AM consent screen. Scopes are not displayed on the consent screen by default. You can either configure clients to use implied consent, or configure the scopes that should be displayed.
Because scope names are arbitrary, they might not be descriptive enough for the resource owner to understand their purpose. In addition, you might not want resource owners to see a particular scope that is for internal use only.
Display scopes in the consent screen
You can configure the AM consent screen to show, for each scope, one of the following options:
| The scope itself | A localized description | Neither the scope nor a description |
|---|---|---|
|
|
|
Configure how scopes appear in the consent screen by client or by realm (in the OAuth 2.0 provider service).
For examples, refer to the Client Registration Scope Allowlist field in the provider’s Advanced reference section or the Scope(s) field in Core Properties.
| Client-level configuration overrides the configuration set at the provider level. |
Special scopes
AM reserves the following special scopes that cannot be added during dynamic client registration:
- am-introspect-all-tokens
-
Add this scope to the Scopes(s) field in a client profile to let the client introspect tokens issued to other clients, as long as all clients are registered in the same realm.
For example:
-
Client A is registered in the
/customers/NArealm, and it is issued a token there. -
Client B is registered in the
/customersrealm. It cannot introspect Client A’s token because they are not in the same realm. Client B can only introspect tokens from other clients registered in the/customersrealm.
-
- am-introspect-all-tokens-any-realm
-
Add this scope to the Scopes(s) field in a client profile to let the client introspect tokens issued to other clients, as long as they are registered in the realm of the introspecting client, or in a subrealm of it.
For example:
-
Client A is registered in the
/customers/NArealm, and it is issued a token there. -
Client B is registered in the
/customersrealm. It can introspect Client A’s token because the/customers/NArealm is a subrealm of the/customersrealm.Client B can introspect tokens for any client registered in the
/customerrealm, or any subrealm of it.
-
For security reasons, give these scopes only to the clients that need them.
Related information:
-
For examples of requesting scopes from the authorization server, refer to any of the grant flows in OAuth 2.0 grant flows.
-
To create your own implementation of the scope handler, refer to Customize OAuth 2.0.
-
To configure AM to grant scopes dynamically by evaluating authorization policies at runtime, refer to Authorization and policy decisions and Dynamic OAuth 2.0 authorization.