Where to go from here
IDM can do much more than reconcile data between two different sources. Read about the key product features in these sections:
Reconciliation
IDM supports reconciliation between two data stores, as a source and a target.
In identity management, reconciliation compares the contents of objects in different data stores, and makes decisions based on configurable policies.
For example, if you have an application that maintains its own user store, IDM can ensure your canonical directory attributes are kept up to date by reconciling their values as they are changed.
For more information, refer to Synchronization overview.
Authentication Modules
IDM provides several authentication modules to help you protect your systems. For more information, refer to Authentication and session modules.
Password Management
Administrative users can manage user passwords from the admin UI, and users can reset their own passwords in the End User UI.
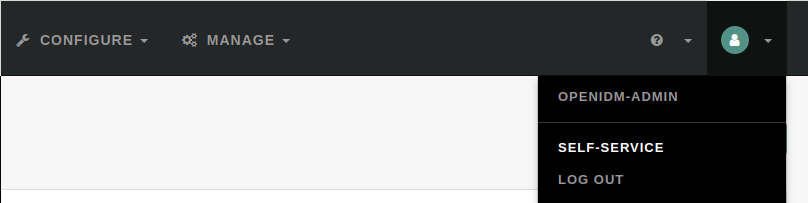
To access the End User UI as an administrative user, log in to the admin UI, and select Self-Service from the drop-down menu in the top right corner:
In the End User UI, click Edit Your Profile, and click Reset next to the Password field. You can change your password, subject to the following minimum number of characters:
-
Length ≥ 8
-
Capital letters ≥ 1
-
Numbers ≥ 1
IDM supports robust password policies. You can modify policies such as the following:
-
Elements that should not be a part of a password, such as a family name
-
Password expiration dates
-
Password histories, to prevent password reuse
For more information, including details on configuring these policies, refer to Passwords.
User Role Management
Some users need accounts on multiple systems. For example, insurance agents may also have insurance policies with the company that they work for. In that situation, the insurance agent is also a customer of the company.
Alternatively, a salesperson may also test customer engineering scenarios. That salesperson may also need access to engineering systems.
Each of these user scenarios is known as a role. You can set up a consolidated set of attributes associated with each role. To do so, you would configure custom roles to assign to selected users. For example, you may assign both insured and agent roles to an agent, while assigning the insured role to all customers.
In a similar fashion, you can assign both sales and engineering roles to the sales engineer.
You can then synchronize users with those roles into appropriate data stores.
For more information, refer to Managed Roles. For a sample of how you can configure external roles, refer to Provision users with roles.
Business Processes and Workflows
A business process begins with an objective and includes a well-defined sequence of tasks to meet that objective. IDM allows you to configure many of these tasks as self-service workflows, such as self-registration, new user onboarding, and account certification.
You can also automate many of these tasks as a workflow.
After you configure the right workflows, a newly hired engineer can log in to IDM and request access to manufacturing information.
That request is sent to the appropriate manager for approval. After it is approved, IDM provisions the new engineer with access to manufacturing.
IDM supports workflow-driven provisioning activities, based on the embedded Flowable Process Engine, which complies with the Business Process Model and Notation 2.0 (BPMN 2.0) standard.
Remote Data Stores
IDM can connect to a substantial variety of user and device data stores, on premise and in the cloud. A number of specific connectors are provided, allowing you to connect to those dedicated data stores. In addition, you can connect to many more data stores using a scripted connector framework.
Connectors are provided for a number of external resources, including:
-
Google Web Applications (refer to Google Apps connector).
-
Salesforce (refer to Salesforce connector).
-
Any LDAPv3-compliant directory, including DS and Active Directory (refer to LDAP connector).
-
CSV Files (refer to CSV file connector).
-
Database Tables (refer to Database table connector).
For a full list, refer to Supported connectors.
If the resource that you need is not on the list, you should be able to use one of the scripted connectors to connect to that resource:
-
For connectors associated with Microsoft Windows, IDM includes a PowerShell Connector Toolkit that you can use to provision a variety of Microsoft services, including but not limited to Active Directory, SQL Server, Microsoft Exchange, SharePoint, Azure Active Directory, and Office 365. For more information, refer to Powershell connector. IDM includes a sample PowerShell Connector configuration, described in Connect to Active Directory with the PowerShell connector.
-
For other external resources, IDM includes a Groovy Connector Toolkit that allows you to run Groovy scripts to interact with any external resource. For more information, refer to Groovy Connector Toolkit.
For sample implementations of the scripted Groovy connector, refer to Connect to DS with ScriptedREST.
Additional Samples
IDM is a lightweight and highly customizable identity management product.
The documentation includes a number of additional use cases. Most of these are known as Samples, and are described in Samples provided with IDM.
These samples include step-by-step instructions on how you can connect to different data stores, customize product behavior using JavaScript and Groovy, and administer IDM with ForgeRock’s common REST API commands.