OATH Token Verifier node
Requests and verifies a one-time password (OTP) generated by a device such as a mobile phone.
The default configuration is time-based OTP (TOTP), but the node also supports HMAC (HOTP).
The node requires that the user credentials are authenticated, and that the user has previously registered a device using the OATH Registration node. These two nodes work together to provide all the capabilities of a secure OATH authentication journey.
You can also use them with other MFA nodes such as the following to extend these capabilities:
|
You can use the OATH nodes in conjunction with the ForgeRock Authenticator application to register your phone, receive notifications, or generate one-time passwords. |
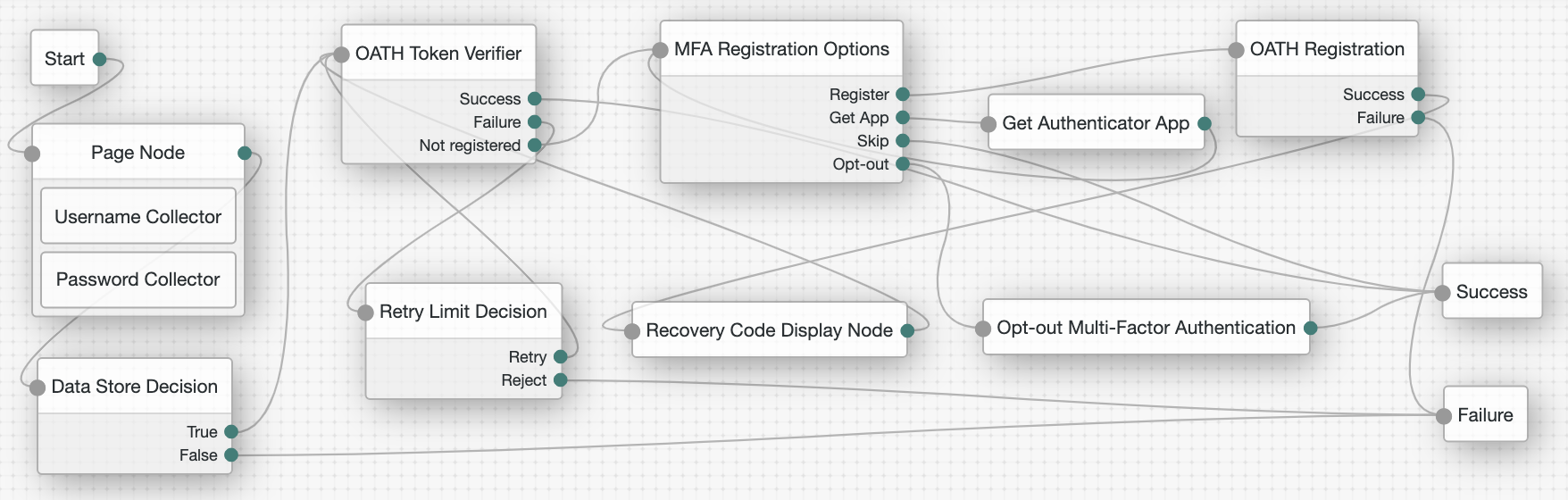
Outcomes
Evaluation continues along one of the following outcome paths:
Success-
There is a registered device and the token code is verified.
Failure-
The user is not authenticated, or the collected token code cannot be verified.
Not registered-
There is no registered device for the user.
Properties
| Property | Usage |
|---|---|
OATH Algorithm |
Specify the algorithm your device uses to generate the OTP:
If this is set to HOTP, you need to set the same value in the OATH Registration node. |
HOTP Window Size |
This property sets the window that the OTP device and the server counter can be out of sync. For example, if the window size is 100 and the server’s last successful login was at counter value 2, the server accepts an OTP that is generated between counter 3 and 102. The default value is 100. |
TOTP Time Step Interval |
The length of time that an OTP is valid, in seconds. For example, if the time step interval is 30 seconds, a new OTP is generated every 30 seconds, and is valid for 30 seconds only. The default value is 30. |
TOTP Time Steps |
This is the number of time step intervals that the OTP is permitted to be out of sync. This applies to codes that are generated before or after the current code. For example, with a time step of 1, the server permits either the previous, the current, or the next code. The default value is 2. |
TOTP Hash Algorithm |
The HMAC hash algorithm to be used to generate the OTP codes. ForgeRock Authenticator (OATH) supports SHA1, SHA256, and SHA512. |
TOTP Maximum Allowed Clock Drift |
Number of time steps a client can be out of sync with the server before manual resynchronization is required. For example, with 3 allowed drifts and a time step interval of 30 seconds, the server allows codes from up to 90 seconds from the current time to be treated as the current time step. The drift for a user’s device is calculated each time they enter a new code. If the drift exceeds this value, the user’s authentication code is rejected. The default value is 5. |
Allow recovery codes |
Specify whether to allow users to use one of the recovery codes to proceed with the login. |