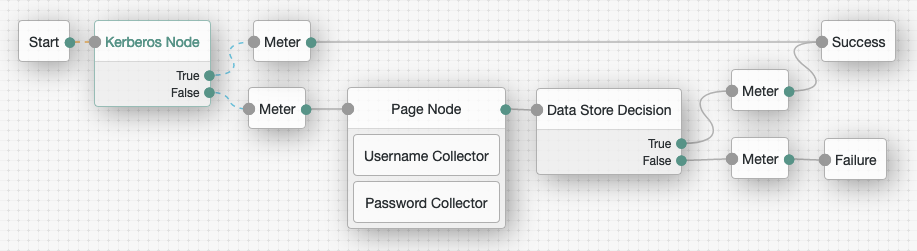
Kerberos node
Enables desktop single sign-on such that a user who has already authenticated with a Kerberos Key Distribution Center can authenticate to AM without having to provide the login information again.
To achieve this, the user presents a Kerberos token to AM through the Simple and Protected GSS-API Negotiation Mechanism (SPNEGO) protocol.
End users may need to set up Integrated Windows Authentication in Internet Explorer or Microsoft Edge to benefit from single sign-on when logged on to a Windows desktop.
Outcomes
-
True -
False
Evaluation continues along the True path if Windows Desktop SSO is successful;
otherwise, evaluation continues along the False path.
Properties
| Property | Usage | ||
|---|---|---|---|
Service Principal |
Specifies the Kerberos principal for authentication in the format In multi-instance AM deployments, configure AM-DOMAIN as the FQDN or IP address of the load balancer in front of the AM instances. For example, For more information, refer to the KB article How do I set up the WDSSO authentication module in AM in a load-balanced environment?. |
||
Key Tab File Path |
Specifies the full, absolute path of the keytab file for the specified Service Principal.
|
||
Kerberos Realm |
Specifies the name of the Kerberos (Active Directory) realm used for authentication. Must be specified in ALL CAPS. |
||
Kerberos Server Name |
Specifies the fully qualified domain name, or IP address of the Kerberos (Active Directory) server. |
||
Trusted Kerberos realms |
Specifies a list of trusted Kerberos realms for user Kerberos tickets. If realms are configured, then Kerberos tickets are only accepted if the realm part of the user principal name of the user’s Kerberos ticket matches a realm from the list. Each trusted Kerberos realm must be specified in all caps. |
||
Return Principal with Domain Name |
When enabled, AM returns the fully qualified name of the authenticated user rather than just the username. |
||
Lookup User In Realm |
Validates the user against the configured data stores.
If the user from the Kerberos token is not found, evaluation continues along the This search uses the |
||
Is Initiator |
When enabled ( When disabled ( |