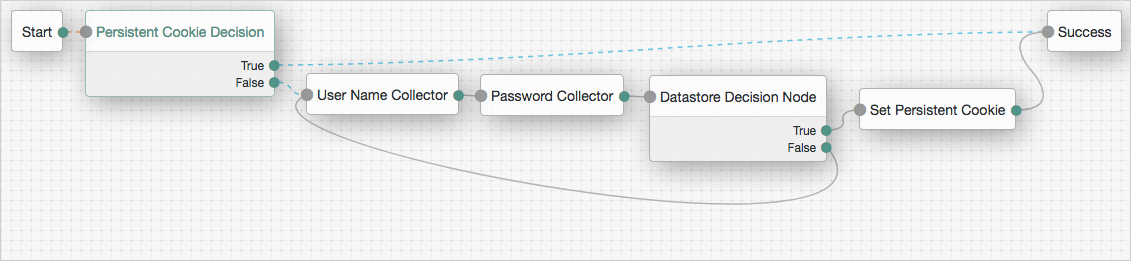
Persistent Cookie Decision node
Checks for the existence of a specified persistent cookie, the default being session-jwt.
If the cookie is present, the node verifies the signature of the JWT stored in the cookie with the signing key specified in the HMAC signing key property.
If the signature is valid, the node decrypts the payload of the JWT. It uses the key pair specified in the Persistent Cookie Encryption Certificate Alias property, found in the AM admin UI under Realms > Realm Name > Authentication > Settings > Security. The global level is found under Configure > Authentication > Core Attributes > Security.
The decrypted JSON payload includes information, such as the UID of the identity and the client IP address. Enable Enforce Client IP to verify that the current IP address and the client IP address in the cookie are identical.
|
This node recreates the received persistent cookie, updating the value for the idle time property. Cookie creation properties for the Set Persistent Cookie node are therefore available in this node as well. |
Outcomes
-
True -
False
Evaluation continues along the True outcome path
if the persistent cookie is present and all the verification checks above are satisfied;
otherwise, evaluation continues along the False outcome path.
Properties
| Property | Usage | ||
|---|---|---|---|
Idle Timeout |
Specifies the maximum amount of idle time allowed before the persistent cookie is invalidated, in hours. If no requests are received and the time is exceeded, the cookie is no longer valid. |
||
Enforce Client IP |
When enabled, ensures that the persistent cookie is only used from the same client IP to which the cookie was issued. |
||
Use Secure Cookie |
When enabled, adds the If the |
||
Use HTTP Only Cookie |
When enabled, adds the When the |
||
HMAC Signing Key (required) |
Specifies a key to use for HMAC signing of the persistent cookie. Values must be base64-encoded and at least 256 bits (32 bytes) long.
To generate an HMAC signing key, run one of the following commands: bash or bash |
||
Persistent cookie name |
Specifies the name of the persistent cookie to check. |