Manage consent
Many OAuth 2.0 and OIDC flows require user consent to grant the client access to the user’s resources.
Implied consent
By default, OAuth 2.0 and OIDC client applications in Identity Cloud use implied consent; Identity Cloud does not prompt for consent during authorization flows. This simplifies the flows. The user has only to sign on to grant the client access to protected resources.
A client application may opt to disable implied consent, however, and prompt the user explicitly:
-
In the Identity Cloud admin UI, go to Applications > Client ID > Sign On > General Settings > Show advanced settings > Authentication.
-
Clear Implied Consent.
-
Save your changes.
Gather consent
If you opt to require explicit consent, configure how the client application appears to the user.
-
Customize the built-in Identity Cloud End User UI consent screen:
-
In the Identity Cloud admin UI, go to Applications > Client ID > Sign On > General Settings > Show advanced settings > Consent Screen.
-
Update the applicable fields:
- Display Name
-
Display this name to the user when prompting for consent.
- Display Description
-
Explain the decision to the user when prompting for consent.
- Privacy Policy URI
-
Add for the client applications privacy policy.
-
Save your work.
-
-
Delegate consent gathering to another service.
For details, refer to Remote consent service.
Display scopes
Users grant consent based on scopes.
Scopes restrict what is shared with the client and limit what the client can do with the user’s data.
In OAuth 2.0, the meanings of scopes depend on the implementation.
In OpenID Connect, scopes map to standard user data claims;
for example, the profile scope requests access to the user’s default profile claims.
If you opt to require explicit consent and use the built-in Identity Cloud End User UI consent screen, configure how the consent screen displays scopes and claims. For details, refer to Display scopes in the consent screen.
Store consent decisions
If you opt to require explicit consent, Identity Cloud can store the consent decisions in the user profile. This minimizes redundant prompts and improves the user experience.
When an OAuth 2.0 client application requests scopes, Identity Cloud checks the user profile for scopes the user has already consented to. Identity Cloud does not prompt the user to consent again to the same scopes, only scopes the user has not consented to.
To save consent:
-
Add an attribute, such as
custom_consent, to user profiles for saving consent decisions.The attribute must be of type
array.For instructions on adding the attribute, refer to Customize user identities.
-
Under Native Consoles > Access Management, go to Realms > Realm Name > Services > OAuth2 Provider and select the Consent tab.
-
In the Saved Consent Attribute field, add the name of the attribute you created, such as
custom_consent. -
Save your changes.
To force Identity Cloud to prompt for consent for a specific client request, add the prompt=consent parameter.
|
Revoke consent
You can revoke a client application’s access at any time through the Identity Cloud End User UI:
-
Sign on as an end user.
Your dashboard page displays.
-
Click Edit Your Profile.
-
Under Authorized Applications, expand the application’s entry.
-
Click Revoke Access:
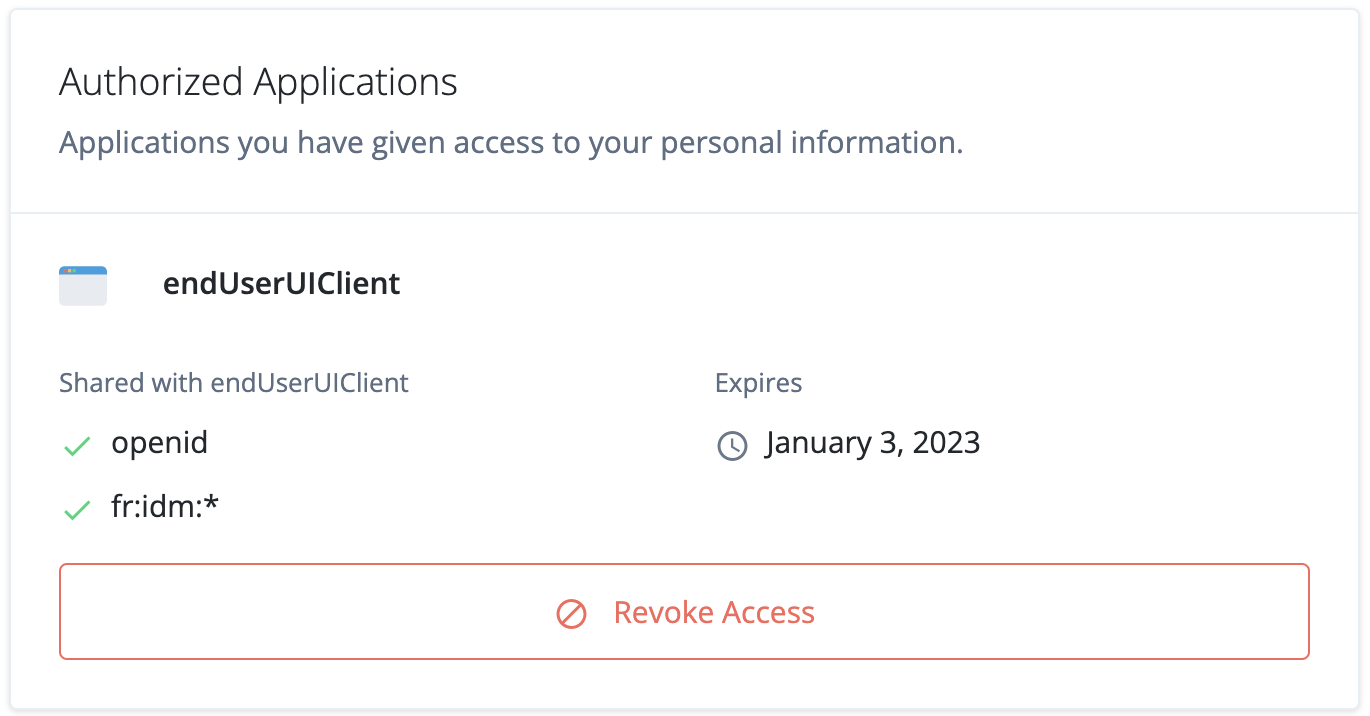 Figure 1. Authorized Applications pane
Figure 1. Authorized Applications pane