Roles and assignments
Roles and assignments let you create an entitlements structure that fits the needs of each realm in PingOne Advanced Identity Cloud.
Identity architects usually build the entitlements structure, and may also use the native AM and IDM consoles to put more complex entitlements in place.
Once your entitlements structure is in place, you can use the Advanced Identity Cloud admin console to:
-
Add new user profiles, device profiles, or roles
-
Add assignments to roles
-
Make changes to existing user profiles, device profiles, roles, or assignments
-
Provision identities with role-based permissions
Roles
Roles define privileges for user and device identities. Roles let you automatically update privileges in numerous identity profiles. All role members receive the same permissions you’ve defined for the role. When you change the privileges for that role, you change the permissions for all role members.
When you add a role to an identity profile, the user or device becomes a member of the role. A user or device can belong to many roles.
A role won’t work until you link it to at least one assignment. During the authorization process, Advanced Identity Cloud evaluates permissions based on:
-
Roles a user or device belongs to
-
Assignments attached to their roles
Internal roles
Internal roles, also called authorization roles, control access to your identity platform. You use internal roles to authorize administrators to manage your tenant or identities contained in it.
External roles
External roles, also called provisioning roles, give users and devices the permissions they need to access apps and services. You use external roles to let employees access intranet applications. You can also use external roles to let your customers and their end users access web services and mobile apps in your tenant.
Assignments
You create an assignment when you want to give a user or device permission to access a resource they need to do a job. A resource might be any application or service, data contained in a document or a database, or a device such as a printer or cell phone.
An assignment won’t work without a role. A role-assignment relationship is not fully formed until you do two things:
Assignment linked to role
Link an assignment to a role. Advanced Identity Cloud grants the permissions defined in the assignment to all members of the linked role.
Assignment mapped to attribute
Map your tenant assignment to an attribute stored in an external system. An external system can be, for example, an intranet Reporting App with its own database of user accounts.
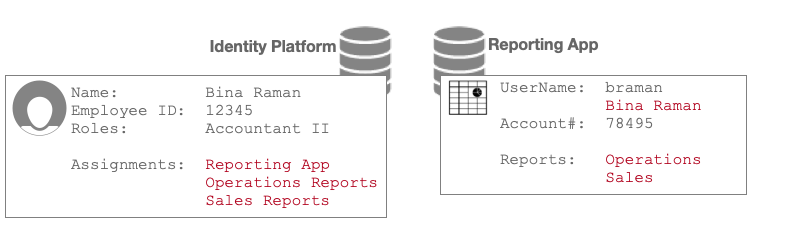
In this illustration, Bina’s Accountant II role links to three assignments. During data store sync, Advanced Identity Cloud provisions her Reporting App user account based on assignment-attribute mappings:
| Mapping From Assignment Attribute | Mapping To Reporting App | Description and Provisioning Outcome |
|---|---|---|
Assignments: Reporting App |
UserName |
The mapping sets the value of Bina’s Name ("Bina Raman") in the UserName attribute in the Reporting App. |
Assignments: Operations Reports |
Reports: Operations |
The mapping adds the value "Operations" to the Reports attribute in the Reporting App. |
Assignments: Sales Reports |
Reports: Sales |
The mapping adds the value "Sales" to the Reports attribute in the Reporting App. |
You can create any number of assignments in your tenant. You can link an assignment to one or more external roles. You cannot link assignments to internal roles.
How provisioning works
When you add a user or device to a role, Advanced Identity Cloud updates the user or device profile with the role information. The update gives, or provisions, the user or device with the permissions that come with the role and its assignments.
Here’s a simple entitlement schema example:
- Roles
-
Accountant-I
Accountant-II - Accountant-I Assignments
-
Reporting App
Operations Reports - Accountant-II Assignments
-
Reporting App
Operations Reports
Sales Reports
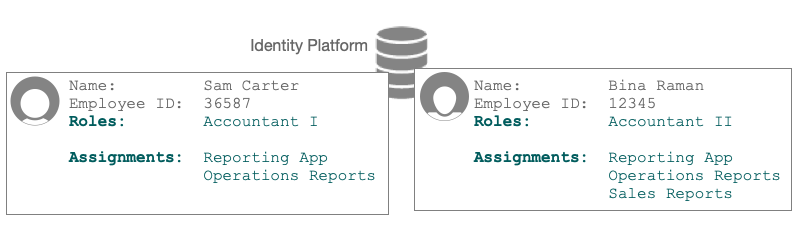
Sam and Bina are co-workers. Their identity profiles are provisioned with permissions based on the entitlements schema example.
-
Sam is a member of the Accountant I role.
The Accountant I role assignments give Sam permission to use the Reporting app to access only Operations Reports. -
Bina is a member of the Accountant II role.
The Accountant II role assignments give Bina permission to use the Reporting app to access both Operations Reports and Sales Reports.
|
For a deep dive, learn more in the following documents: |