Policies in the UI
You manage policies under Native Consoles > Access Management. Go to Realms > Realm Name > Authorization > Policy Sets and select the name of the policy set in which to configure a policy.
| To... | Action |
|---|---|
Create a policy |
Click Add a Policy. When creating a policy, specify a name, a resource type, and at least one resource. Click Create. |
Modify a policy |
Click the policy name or the pencil icon (). |
Delete a policy |
Click the delete icon () or click the policy name then x Delete. |
Policy type names
Do not use any of the following characters in policy, policy set, or resource type names:
Double quotes (")
Plus sign (+)
Comma (,)
Less than (<)
Equals (=)
Greater than (>)
Backslash (\)
Forward slash (/)
Semicolon (;)
Null (\u0000)
Resources
To define resources that the policy applies to:
-
Click the Resources pencil icon () or the Resources tab.
-
Select a resource type from the Resource Type drop-down list.
The resource type determines which resource patterns are available. The
OAuth2 Scoperesource type contains the same resource patterns as theURLresource type, as well as the*pattern.Use the resource patterns that are most relevant for the scopes in your environment.
For information on configuring resource types, refer to Resource types.
-
Select a resource pattern from the Resources drop-down list.
-
Replace the asterisks with values for matching resources, and click Add.
For information on configuring resource patterns, refer to Resource type patterns.
-
Optionally, click Add Resource to add further resource patterns, or click () to delete a resource pattern.
-
Save your changes.
Policy actions
To define policy actions that allow or deny access to a resource:
-
Click the Actions pencil icon () or the Actions tab.
-
Click Add an Action to select an action from the drop-down list.
-
Select whether to allow or deny the action on the resources.
-
Optionally, add further actions, or click () to delete actions.
-
Save your changes.
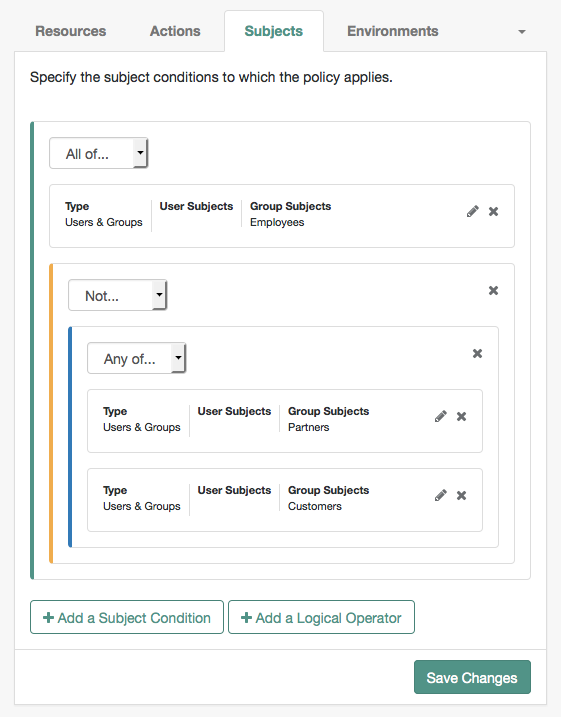
Conditions
To define subject and environment conditions:
-
Combine logical operators with blocks of configured parameters to create a rule set. The policy uses this rule set to filter requests for resources.
-
Use drag and drop to nest logical operators at multiple levels to create complex rule sets.
-
A gray horizontal bar indicates a valid point to drop a block.
Subjects
To define the subject conditions that the policy applies to:
-
Click Add a Subject Condition, choose the type from the drop-down menu, and provide any required subject values.
-
When complete, click the check icon () and drag the block into a valid drop point in the rule set.
-
To add a logical operator, click Add a Logical Operator, choose between
All Of,Not, andAny Offrom the drop-down list, and drag the block into a valid drop point in the rule set. -
To edit a condition, click the edit icon (), or click () to delete.
-
Continue combining logical operators and subject conditions and click Save Changes when you’ve finished.
| Subject condition types | Description |
|---|---|
Authenticated Users |
Any user that has successfully authenticated with PingOne Advanced Identity Cloud. |
Users & Groups |
Search for and select one or more users or groups under the Realms > Realm Name > Identities or the Groups tab. |
OpenID Connect/Jwt Claim |
Validate a claim within a JSON Web Token (JWT). Type the name of the claim to validate in the Claim Name field, for example, Repeat the step to enter additional claims. The claim(s) will be part of the JWT payload together with the JWT header and signature. The JWT is sent in the authorization header of the bearer token. This condition type only supports string equality comparisons, and is case-sensitive. |
Never Match |
Never match any subject. This disables the policy. If you do not set a subject condition, To match regardless of the subject, configure a |
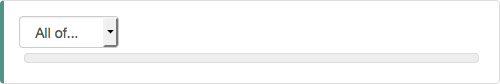
Environments
To define the environment conditions the policy applies to:
-
Click Add an Environment Condition, choose the type from the drop-down menu, and provide any required subject values.
Scriptis the only environmental condition available for OAuth 2.0 policies. -
When complete, click the check icon () button and drag the block into a valid drop point in the rule set.
-
To add a logical operator, click Add a Logical Operator, choose between
All Of,Not, andAny Offrom the drop-down list, and drag the block into a valid drop point in the rule set. -
To edit a condition, click the edit icon (), or click () to delete.
-
Continue combining logical operators and subject conditions and click Save Changes when you’ve finished.
| Environment condition types | Description | ||
|---|---|---|---|
Active Session Time |
Set a condition for the maximum duration the user’s session has been active.
To end the session if it has been active for longer than |
||
Authentication by Module Chain |
Not applicable to Advanced Identity Cloud. |
||
Authentication by Module Instance |
Not applicable to Advanced Identity Cloud. |
||
Authentication Level (greater than or equal to) |
The minimum acceptable authentication level required by the policy. |
||
Authentication Level (less than or equal to) |
The maximum acceptable authentication level required by the policy. |
||
Authentication to a Realm |
Make the policy test the realm to which the user authenticated. A session can only belong to one realm, and session upgrade between realms is not allowed. |
||
Current Session Properties |
Evaluate property values set in the user’s session. Set Ignore Value Case to Specify one or more pairs of session properties and values using the format |
||
Identity Membership |
Make the policy apply if the user’s UUID is a member of
at least one of the AMIdentity objects specified in
|
||
IPv4 Address/DNS Name |
The IP version 4 address from which the request originated. The IP address is taken from the Specify a range of addresses to test against by entering four sets of up to three digits,
separated by periods ( If only one of these values is provided, it is used as a single IP address to match. Optionally, specify a DNS name in DNS Name to filter requests to that domain. |
||
IPv6 Address/DNS Name |
The IP version 6 address from which the request originated. The IP address is taken from the Specify a range of addresses to test against by entering eight sets of four hexadecimal characters,
separated by a colon ( If only one of these values is provided, it is used as a single IP address to match. Optionally, specify a DNS name in Use an asterisk (*) in the DNS name to match multiple subdomains.
For example, |
||
LDAP Filter Condition |
Make the policy test whether the user’s entry can be found using the LDAP search filter you specify in the directory configured for the policy service. |
||
OAuth2 Scope |
Set a condition that an authorization request includes all the specified OAuth 2.0 scopes. Scope names must follow OAuth 2.0 scope syntax described in RFC 6749,
Access Token Scope.
Separate multiple scope strings with spaces, such as The scope strings match regardless of order in which they occur, so The condition is also met when additional scope strings are provided beyond those required to match the specified list.
For example, if the condition specifies |
||
Resource/Environment/IP Address |
Define a complex condition, such as whether the user is making a request from the localhost, and has also authenticated in a particular way. Entries must take the form of an If the The available parameters for the
The IP address can be IPv4, IPv6, or a hybrid of the two.
Example: |
||
Script |
Make the policy depend on the outcome of a JavaScript executed at the time of the policy evaluation. For information on scripting policy conditions, refer to Scripted policy conditions.
|
||
Time (day, date, time, and timezone) |
Make the policy test when the policy is evaluated. The values for day, date and time must be set in pairs that comprise a start and an end. 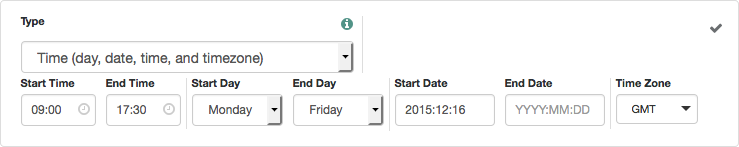
|
||
Transaction |
Make the policy depend on the successful completion of transactional authorization. Transactional authorization requires the user to authenticate for each access to the resource. Transactions support the following authentication strategies:
|
Response attributes
Add user attributes from the identity repository as response attributes—either as subject attribute or static attributes—to the request header at policy decision time.
Note that response attributes are not available for the OAuth2 Scope resource type.
The web or Java agent for the protected resources/applications, or the protected resources/applications themselves, retrieve the policy response attributes to customize the application.
To define response attributes in the policy:
-
Click the Response Attributes edit icon () or the Response Attributes tab.
-
To add subject attributes, select them from the Subject attributes drop-down list.
To remove an entry, select the value, and click Delete (Windows/GNU/Linux) or Backspace (Mac OS X).
-
To add a static attribute, specify the key-value pair for each static attribute. Enter the Property Name and its corresponding Property Value in the fields, and click Add (+).
To edit a static attribute, click the edit icon (), or click () to delete.
-
Continue adding subject and static attributes, and when finished, click Save Changes.
Example
This example policy requires authenticated users to have a session no longer than 30 minutes
to access resources at https://www.example.com:*/*.
|
Before testing your OAuth 2.0 policies, ensure your OAuth 2.0 provider is configured to interact with PingOne Advanced Identity Cloud’s authorization service:
For more information about testing OAuth 2.0 policies, refer to Dynamic OAuth 2.0 authorization. |