PingOne node
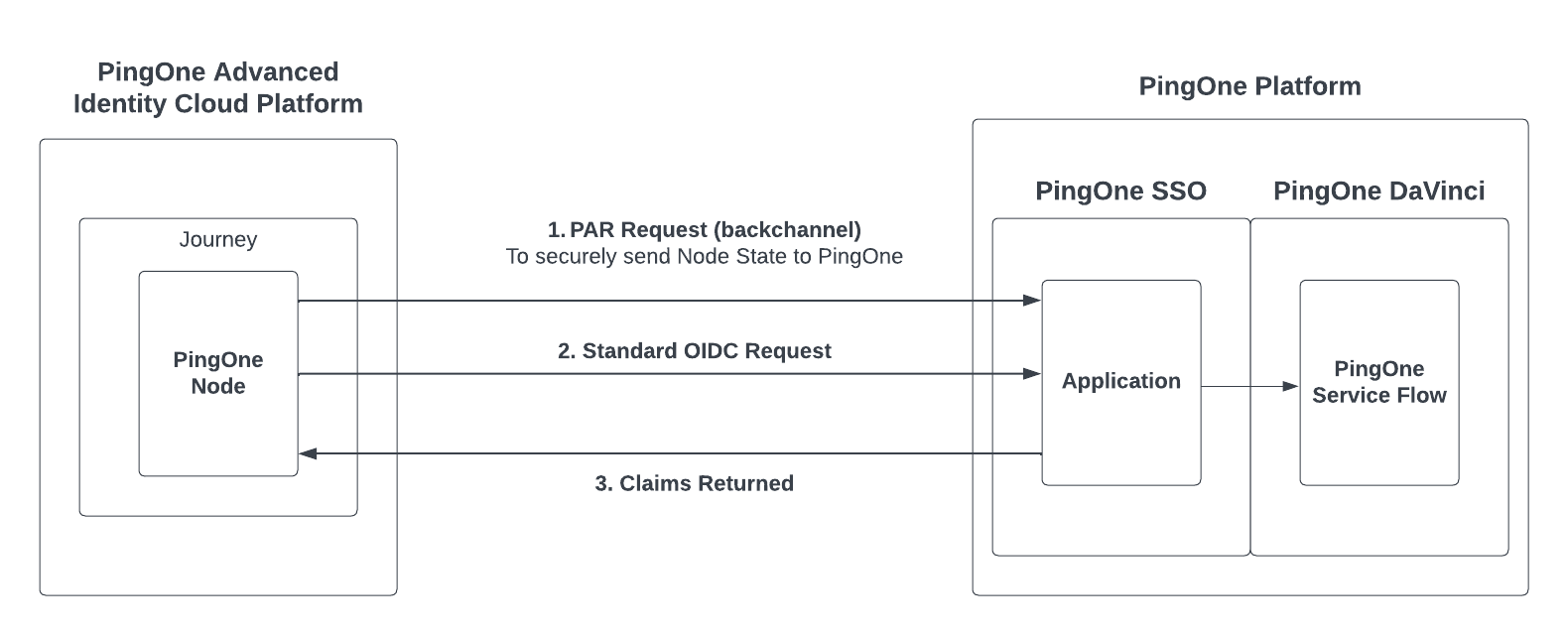
The PingOne node establishes trust between PingOne and Advanced Identity Cloud by leveraging a federated connection.
This node performs an OIDC request to PingOne to delegate the user flow from Advanced Identity Cloud to PingOne using a standard OIDC redirect.
| Use this node only if you need to configure PingOne as an external identity provider for Advanced Identity Cloud or to execute a PingOne DaVinci flow containing UI screens. In all other cases, use the PingOne DaVinci API node instead. |
Set up
Before using the PingOne node, you must set up:
-
Configure a PingOne OIDC application to connect to Advanced Identity Cloud
-
(Optional) If you plan to trigger a DaVinci flow from PingOne node, configure the PingOne application to the DaVinci Flow policy.
Configure a PingOne OIDC application to connect to Advanced Identity Cloud
Use the Applications page in the PingOne interface to add an application to connect to Advanced Identity Cloud.
-
Go to Applications > Applications.
-
Click +.
-
Create an application profile with these parameters:
-
Application name: Advanced Identity Cloud Federation.
-
Description (optional): Enables Advanced Identity Cloud federation with PingOne.
-
Select
OIDC Web Appas the Application Type.
-
-
Click Save.
-
After the application profile is created, go to the Configuration tab and click the pencil icon to edit the application.
-
In the PKCE Enforcement the drop-down, select
S256_REQUIRED. -
In the Token Endpoint Authentication Method drop-down, select
Client Secret Basic. -
Select Require Pushed Authorization Request.
-
Enter the Redirect URIs of your Advanced Identity Cloud AM instance.
-
-
Click Save, and then select Enable.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Configuration
| Property | Usage |
|---|---|
PingOne Service |
The ID of the PingOne Worker service for connecting to PingOne. |
ACR Values(optional) |
For triggering a specific PingOne application policy. |
Username |
The attribute that contains the name of the user for the object. |
State Inputs |
A multi-value field to select specific attributes from node state to include in the federation request to PingOne. By default, the wildcard (*) value includes the entire journey node state in the federation request to PingOne. |
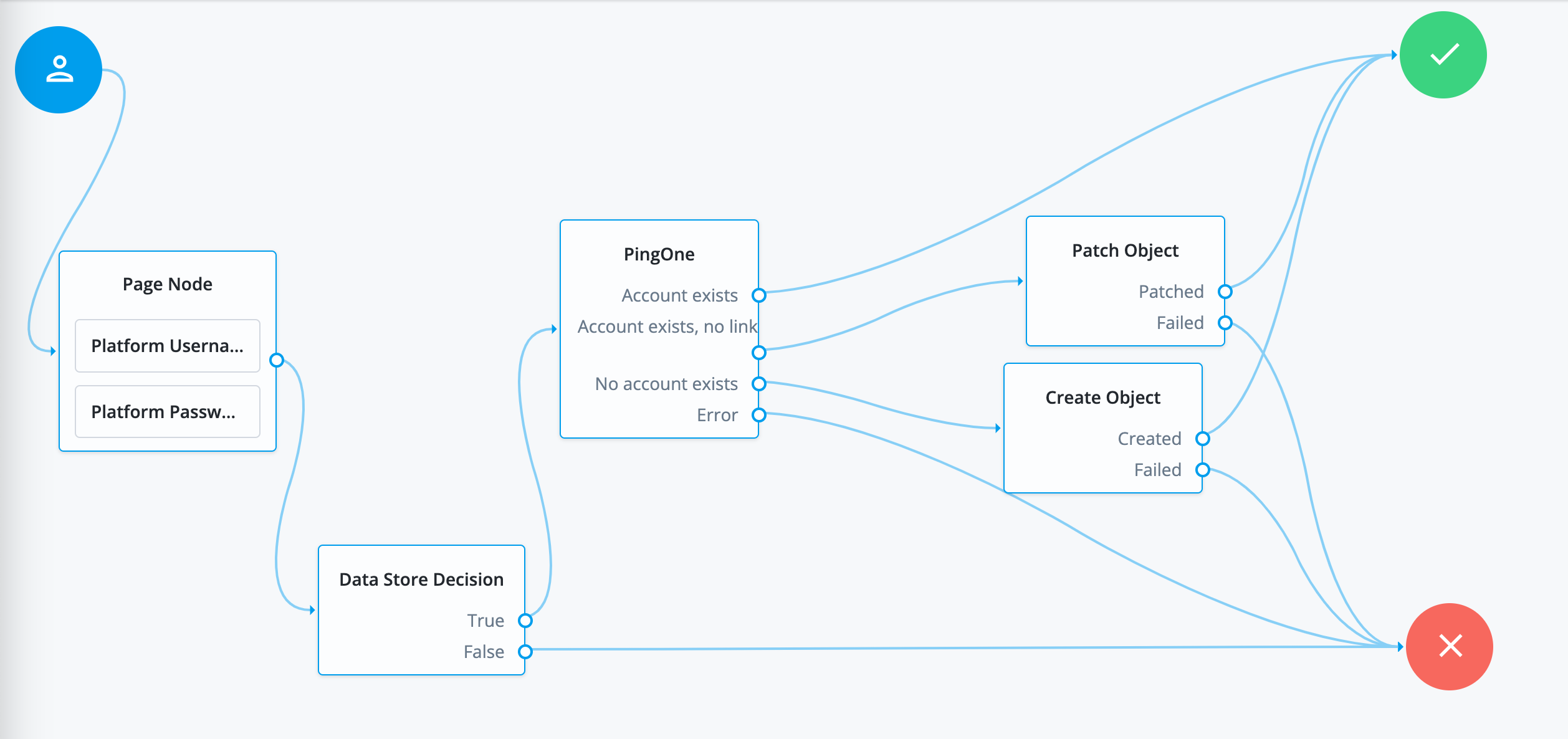
Outcomes
Account exists-
If the account returned by PingOne during federation matches an existing account, and it is linked to the account in Advanced Identity Cloud.
Account exists, no link-
If the account returned by PingOne during federation exists in Advanced Identity Cloud, but it is not yet linked to the existing account in Advanced Identity Cloud.
No account exists-
If the account returned by PingOne during federation does not exist in Advanced Identity Cloud.
Error-
An error occurred causing the request to fail. Check the response code, response body, or logs to see more details of the error.